 About Illegal View
About Illegal ViewIllegal View can be said as on-screen activity trail solution, operation trail solution. and end-point security solution. User can best utilize Illegal View for the following situations; -Prevention of fraudulent operation of IT system/ -Audit trail and non-fraud evidence /-Real-time monitoring/ -End-point security solution against cyber-attack /-Training utilizing recorded on-screen picture / -Work style reform
 Functionality and System Requirement
Functionality and System RequirementIllegal View functionality list and system requirement show that Illegal View provides you with perfect audit trail and non-fraud evidence. Besides, it protects your IT system from internal fraud, cyber-attack. Please review more.
 Collaboration
CollaborationNowadays, many companies deploy SIEM solutions to protect its own IT infrastructure and detect potentially malicious data. Illegal View, with its command prompt function, allows you to realize smooth linkage between the two software as if it were one. Illegal View is now authorized by Hitachi Corporation as certified linkage product for JP1/ Navigation platform.
 About SPIDER
About SPIDERSPIDER is developed only with KDTS's proprietary technology. It is a unique agentless monitoring solution for privileged ID user and regular ID user activity. SPIDER manages activity monitoring via WEB and therefore, it has a minimum network load. SPIDER can be applicable for not only Windows environment but also Linux. Furthermore, it works in thin client environment and VDI environment.
 Functionality and System Requirement
Functionality and System RequirementSPIDER feature and system requirement are listed here and you find all features necessary to manage privileged ID for your IT system's rightful operation.
 Collaboration
CollaborationSPIDER manages ID user activity. With Illegal View linkage, you can record not only ID user activity but also activity contents with recorded on-screen image and various logs such as text, access record and others.
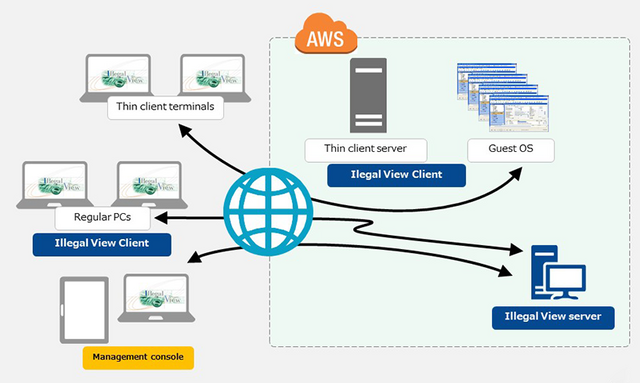
Objective: Effective utilization of Amazon Web service over cloud computing. Illegal View server and Clients are deployed over Cloud computing and are able to record all on-screen data and operation data of both thin client terminals and regular terminals without fail.
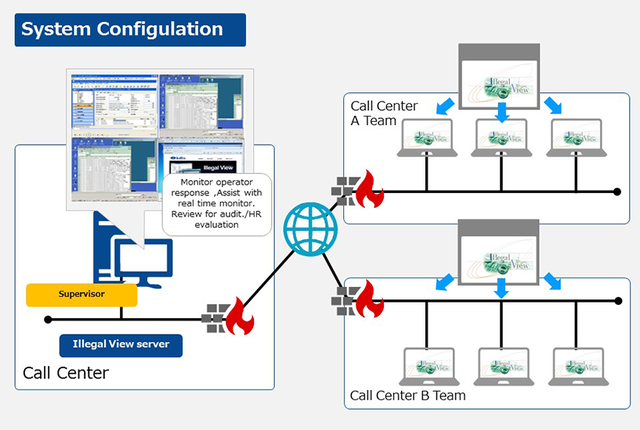
Objective: Quality enhancement of call center total operation skill and help desk operator work 1. To establish fair HR evaluation system for operators by eliminating biased and individualized evaluation by supervisors 2. To increase the number of operator managed by one supervisor
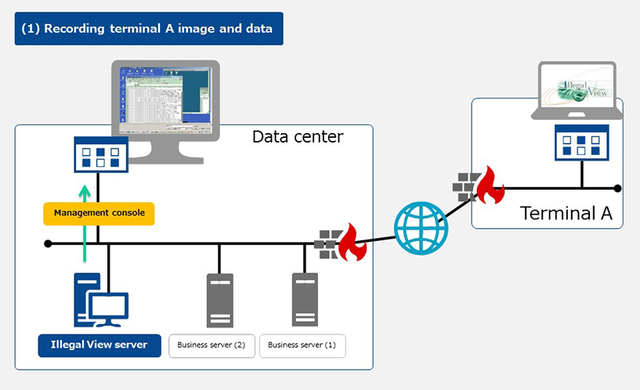
Objective: Server Maintenance Activity Audit Company is obliged to assign monitoring person to witness and monitor the server maintenance work by third party contractor on site to ensure that the work is properly and rightfully conducted. It has incurred a lot of expense and manpower to do this monitoring.
 Products for other countries
Products for other countriesKDTS Co.,Ltd has developed 2 IT hardware products and launched in Thailand to support those Japanese companies who encounter insufficient network infrastructure problem. We believe that these 2 products can also be of great help not only in Thailand but also in other Southeast Asian countries who still have weak and insufficient internet infrastructure.

May 1, 2018

September 4, 2017

July 26, 2017

June 30, 2017
August 31, 2018
June 28, 2018
April 20, 2018

September 1, 2017